Platform audit logs
The platform-level audit log captures every action across every org — far broader scope than per-org audit logs. Useful for security investigations, compliance audits, and platform-wide forensics.
Open platform audit logs
Platform → Audit logs.
You'll see a paginated, filterable, time-ordered log.
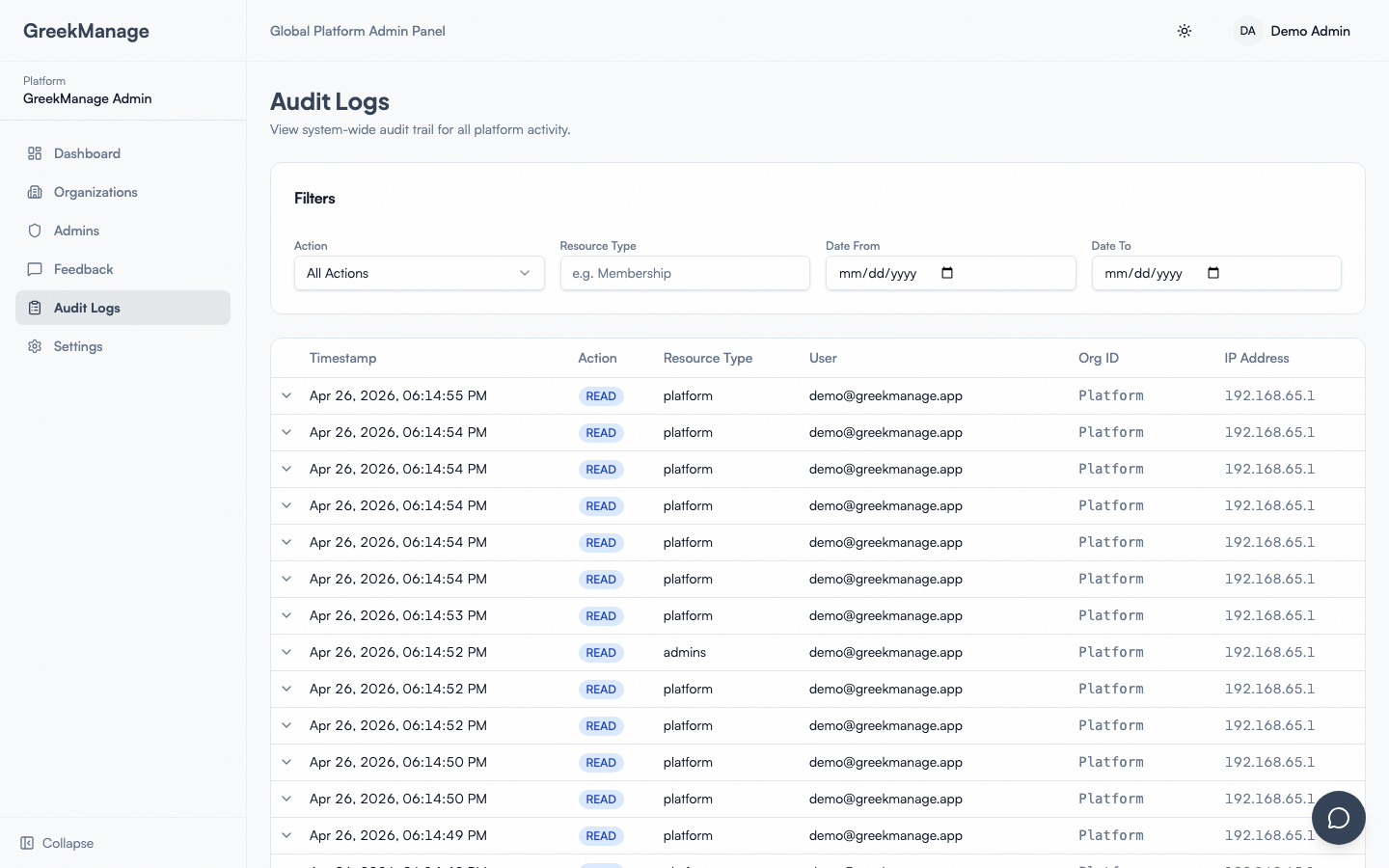 The platform audit log.
The platform audit log.
What's logged at the platform level
Beyond per-org actions:
- Org creation, suspension, activation, deletion
- Platform admin add / remove
- Platform settings changes (email, backups, retention)
- Cross-tenant data access (a platform admin viewing an org's data)
- Backup runs and download events
- Storage migrations
- Password resets initiated by platform admins
- Failed sign-in attempts (for account compromise detection)
Filters
- Date range
- User (any user across any org)
- Action type (e.g.,
org.create,admin.add,data.export) - Org (which tenant)
- IP address
Export
Click Export to download the filtered view as CSV or JSON. JSON preserves nested action context; CSV flattens for spreadsheet use.
Investigation patterns
Suspected account compromise
Filter by:
- User (the affected account)
- Date range (last 30 days)
- Action type (Sign-in, Password change, Profile change)
Look for:
- Sign-ins from unexpected IPs
- Password changes initiated outside expected workflow
- Email changes immediately followed by data export
Suspected admin overreach
Filter by:
- User (the admin in question)
- Action type (Profile edits, Refunds, Bulk operations, Data exports)
Look for:
- Bulk operations on data outside their normal scope
- Refunds without standard chapter approval
- Exports of sensitive data (member PII, financial records)
Unexpected storage usage spike
Filter by:
- Action type (File upload, File delete)
- Date range (the spike window)
Identify which org / user caused the spike.
Retention
Platform audit logs are retained per platform retention policy:
- 2 years for routine actions (default)
- 7 years for security-sensitive actions
- Permanent for cross-tenant access events
Configure in Platform → Settings → Audit retention within applicable legal limits.
Read-only
Platform audit logs are append-only. No one — including platform admins — can edit or delete entries. This is enforced at the database level.
Tips
- Subscribe to anomaly alerts. GreekManage flags unusual patterns (sudden volume of admin actions, off-hours data exports). Configure email notifications in Settings → Audit → Alerts.
- Tag incidents. When investigating an incident, tag relevant log entries for later retrieval.
- Run quarterly audits. Even without an incident, review platform admin actions quarterly. Catch things you didn't notice earlier.